Validation after the fact is no longer sufficient
In many organizations, security is treated as a validation step.
Code is written.
Features are released.
Security reviews happen afterward.
If issues are found, they are fixed.
This model has worked for years. It feels structured. Responsible.
But in a Mendix landscape where applications evolve continuously — and AI-assisted development increases output even further — validation after the fact is no longer sufficient.
Because speed changes the risk equation.
And reaction does not scale with acceleration.
The Reactive Pattern
Most security programs operate on a detection model.
- Vulnerability scans are run periodically.
- Penetration tests are scheduled annually.
- Code reviews are conducted before major releases.
- Findings are tracked and remediated.
The assumption behind this model is simple:
Security risks emerge occasionally.
They are discovered.
They are corrected.
But as delivery frequency increases, the number of changes multiplies. Each release introduces new configuration decisions, new integrations, new access rules.
The surface area of potential misconfiguration expands.
Detection remains periodic.
Change becomes continuous.
That structural imbalance creates exposure windows.
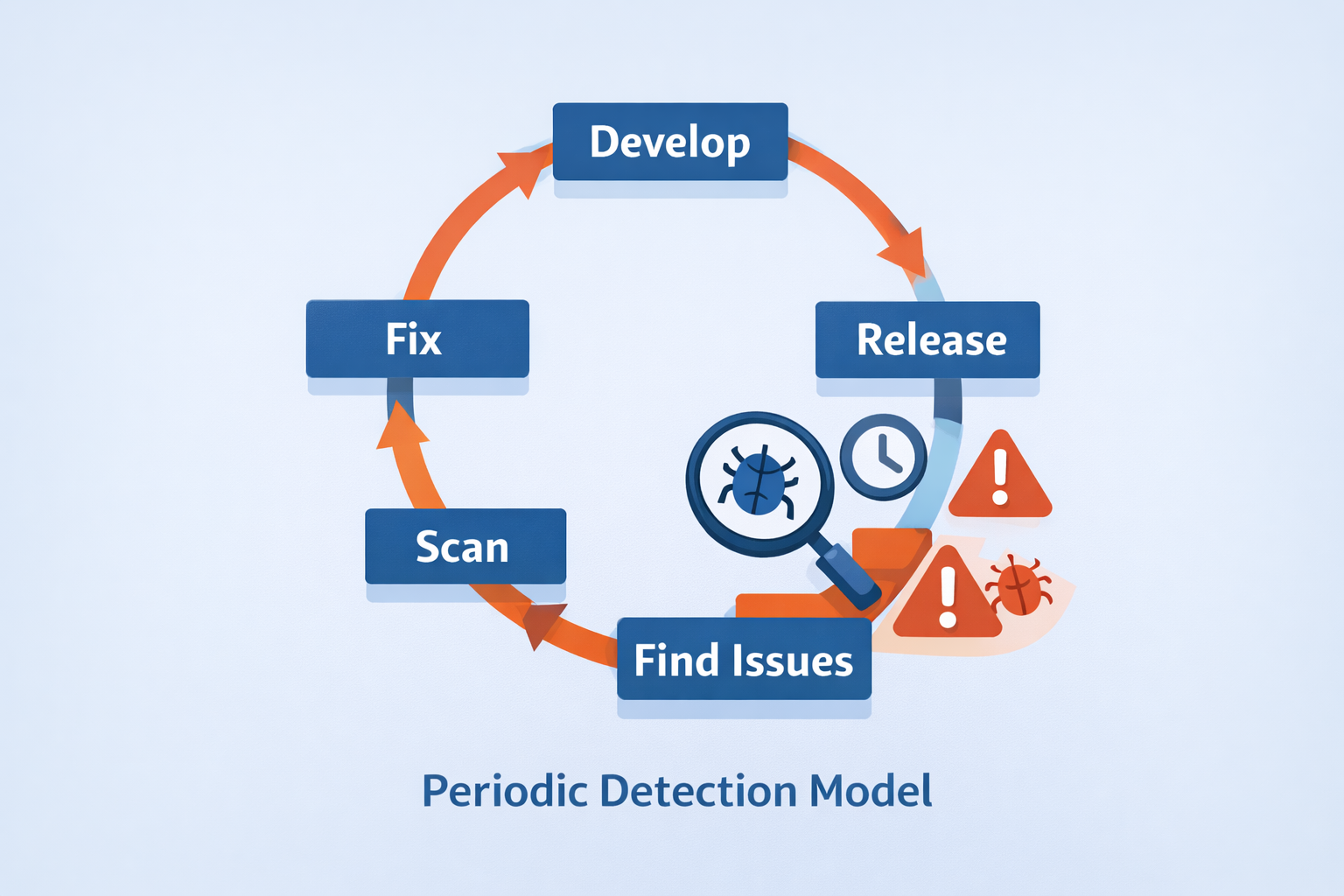
In the traditional reactive security approach, issues are detected periodically after the release is done.
What Secure By Design Really Means
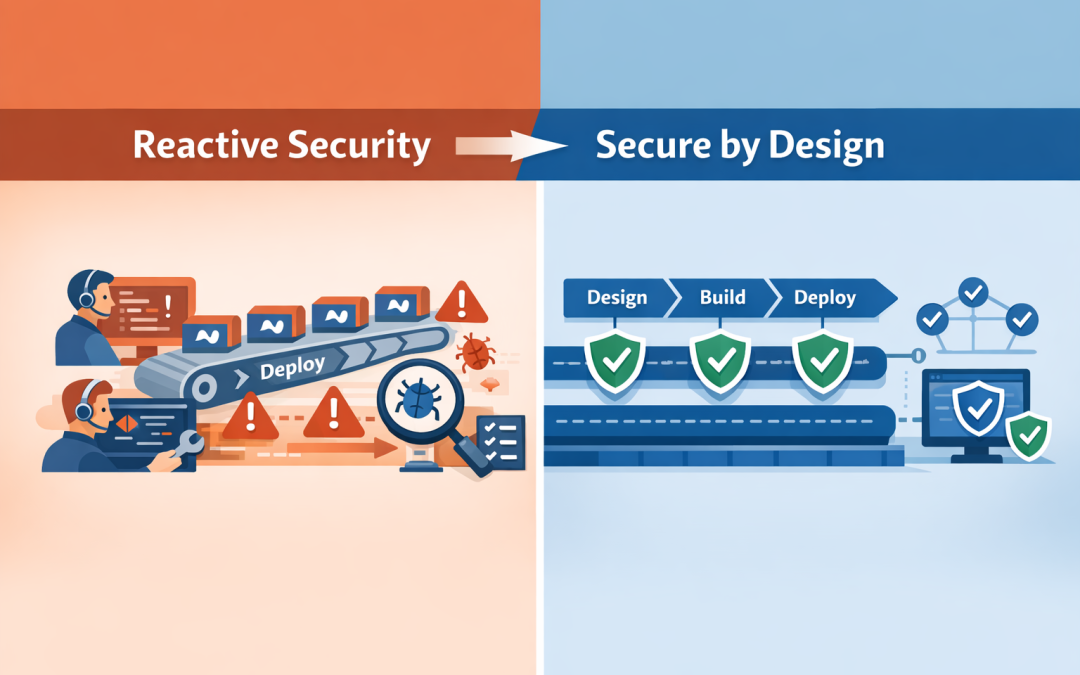
Secure by design is often interpreted as “apply security best practices early.”
That is necessary — but incomplete.
True secure-by-design means that security constraints are embedded directly into the development lifecycle. Not as guidance. Not as documentation. But as enforceable control boundaries.
It means:
- Role models are validated against defined standards.
- Environment segregation is monitored continuously.
- Deployment approvals are enforced structurally.
- Critical configurations cannot drift silently.
Security stops being advisory.
It becomes architectural.
The Illusion of Maturity
Many enterprises believe they are mature because:
- They have security policies.
- They conduct penetration testing.
- They maintain vulnerability registers.
These are important components.
But policies do not enforce themselves.
Reports do not prevent drift.
Findings often surface after exposure has already occurred.
Security maturity is not measured by documentation volume.
It is measured by how little room exists for uncontrolled deviation.
The Mendix Context
Mendix already provides a strong structural foundation:
Explicit domain models.
Managed environment separation.
Centralized deployment flows.
Role-based access management.
These architectural elements create predictability.
But predictability alone does not guarantee adherence to your internal security framework.
Across dozens of applications, subtle variation appears:
- An access role is broadened for convenience.
- A production deployment bypasses a formal review.
- An integration is configured differently from the standard.
Nothing may appear immediately broken.
But risk accumulates quietly.
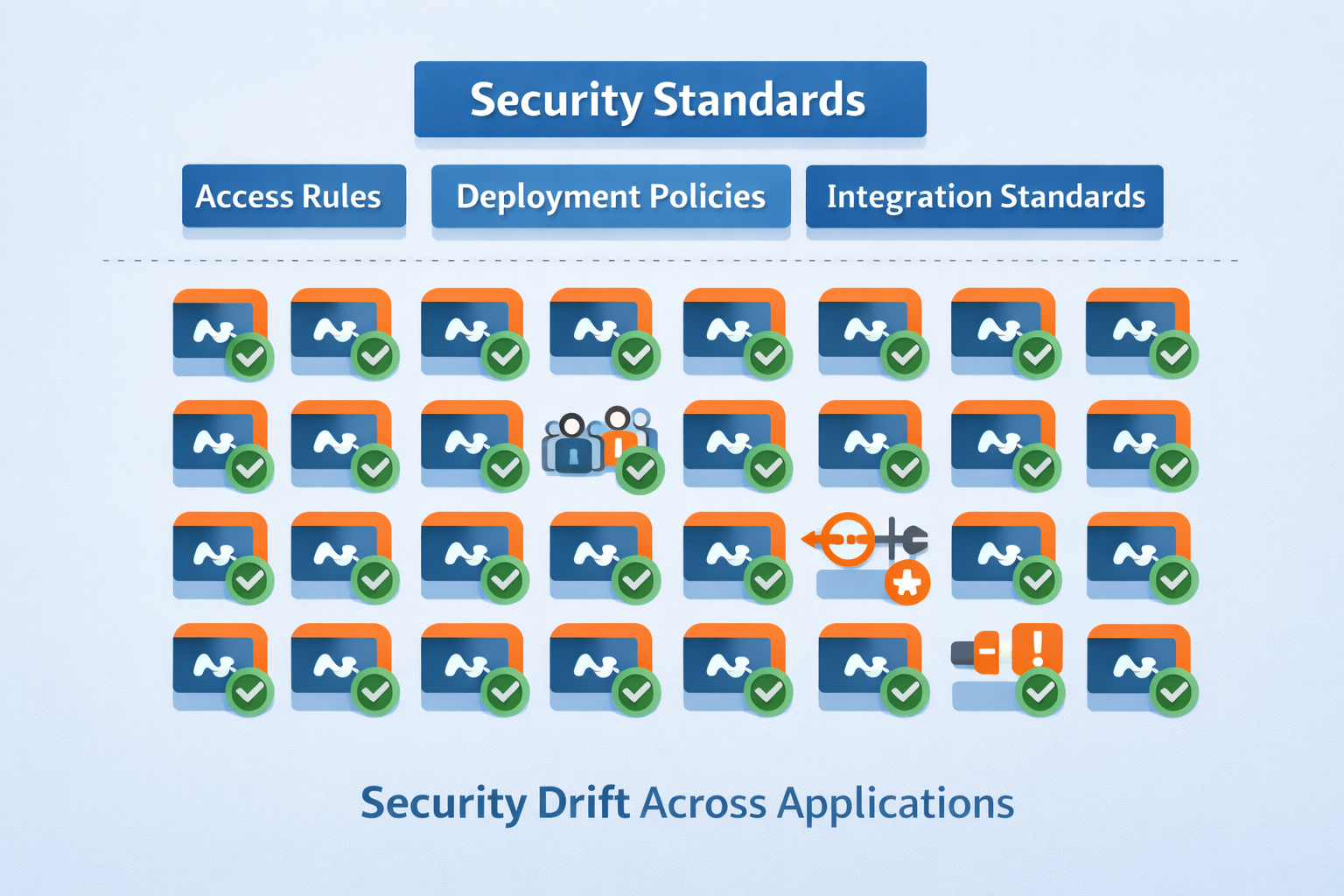
At scale, multiple apps can slowly drfit from your security architecture (domain models, access controls, integration patterns) leading to systemic risk.
Security at Portfolio Scale
Now consider a Mendix portfolio of 75 applications across multiple teams.
Can you answer, in real time:
- Which applications currently comply with your access standards?
- Which deployments were approved by the correct roles?
- Where environment segregation has been altered?
- Which configurations deviate from defined security policies?
If the answer requires manual review, then security assurance is retrospective.
And retrospective assurance cannot keep pace with continuous change.
From Detection to Enforcement
The shift from reactive security to built-in control requires one structural change:
Security must be formalized as enforceable controls.
Each security requirement is defined explicitly.
Each requirement is mapped to measurable validation mechanisms — policy checks, audit events, structured approvals.
Coverage is transparent.
Evidence is generated continuously.
Deviations are visible immediately.
This does not slow development.
It stabilizes it.
Because developers operate within clear boundaries rather than discovering violations later.

When your security standards and architecture are translated into active controls, security by design becomes a continual and operational reality.
Why This Matters Now
AI-assisted development increases throughput.
Low-code platforms reduce friction.
Business expectations accelerate.
The faster applications are built, the less tolerance exists for uncertainty.
Security incidents are no longer isolated technical events. They are board-level issues.
And board-level risk cannot rely on periodic scanning alone.
It requires continuous assurance.
The Real Question
The question is not whether your organization performs penetration testing.
The question is whether your Mendix applications can drift outside your security framework without you knowing.
If security depends on someone discovering a problem later, it is reactive.
If controls are embedded directly into the lifecycle, security becomes structural.
In the next article, we will explore how quality and maintainability determine whether a growing Mendix portfolio becomes a strategic asset — or an operational burden.
Because preventing risk is one dimension of control.
Sustaining long-term adaptability is another.
— Andrew Whalen
Founder, Blue Storm

Recent Comments